Is your Website Or Network secured?! Are you in trouble to stop attacks before they start? In an enterprise or Small business network VAPT (Vulnerability Assessment and penetration Testing) demands a lot more security from an attacker to shatter the integrity of your system. The vulnerability happens because of the fragile password, Improper software settings, Errors in the software and virus in a computer or due to the injection of malicious script or SQL. The better performance is in your hands , delivers you the newest VAPT-network and cyber security solutions and services in Dubai.
The attackers and hacking was there at the development of the internet. But Vulnerability Assessment And Penetration Testing was not utilized so often. Before, there exist networks with trusted nodes, protocols like (SSH, SCP, SSL). Now the important data is transferred via telnet, FTP and plain text HTTP.
Is your data secured in your PC ? Don’t share your information with hackers.Protect yourself while online. Netmate’s VAPT will give you the All in one Protection . VAPT-Network and cyber security solutions and services in Dubai.
DANGER OF HACKING : Where and How these Attacks Happens?
Now a days the attacks happen in the client side. The mainly used attacking methods are sending malicious PDF files, send instant messages and Phishing attacks.Through this the hackers can easily read your private information. They can scan your conversations or chase the back-end of your business or personal website. The precautions for these attacks includes, Use a two way firewall, Regular updating of your computer system, Increasing the browser security using settings and Prevent the use of unwanted and malicious websites links. More than this we provide Cyber security and network security support services in Dubai, Abu dhabi, Ajman, Umm Al Quwain, Sharjah, Ras Al Khaimah and Fujairah.
VULNERABILITY ASSESSMENT AND PENETRATION TESTING (VAPT) WORKFLOW:
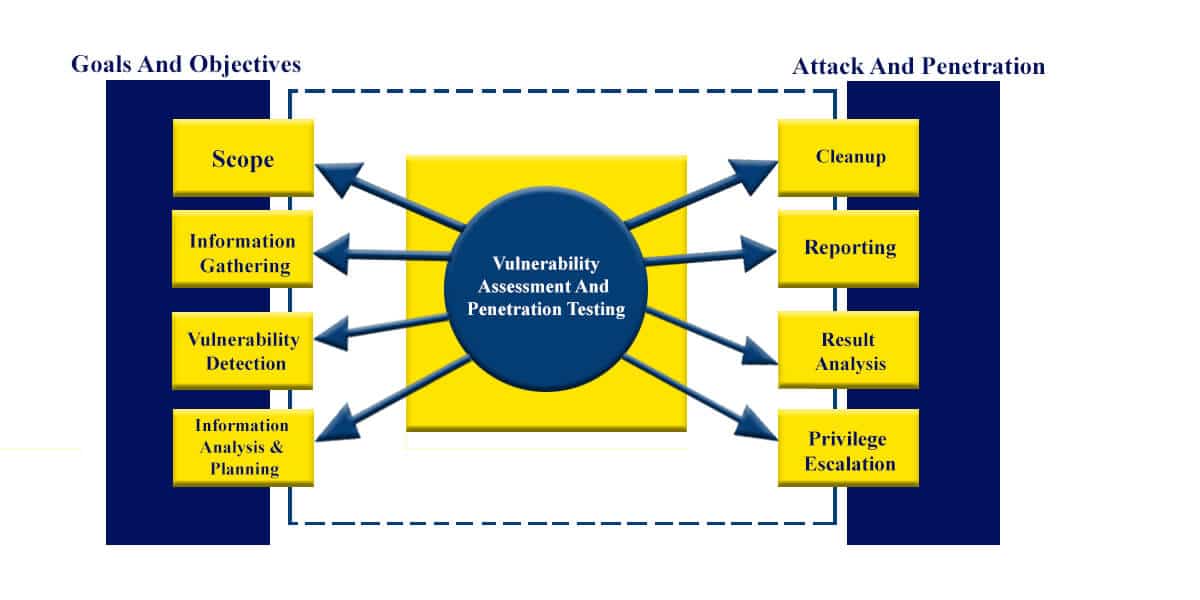
Scope : The following are the possible ways for scope of the assignment
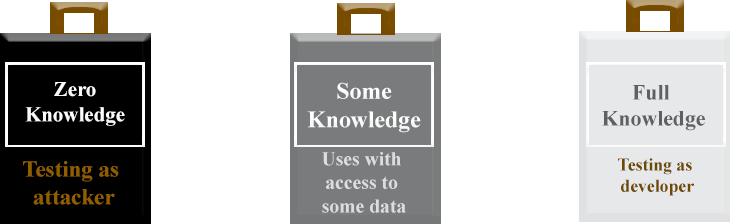
* Black box testing – Testing from an external network with previous knowledge of the internal networks and systems.
* Grey Box Testing – The testing takeplace in either internal or external networks. With the knowledge of the inner network and system.
It is a combination of both Black and white box testing.
* White Box Testing – This is also known as Internal Testing. In this the testing will happen in the internal network.
Information Gathering : Getting the information about IT domain includes, IP address, Networks and Operating system version. It is useful for all three scope of assignment includes, Black box testing, Grey Box testing, White box testing.
Vulnerability Detection : In this process, Vulnerability scanners are used. It will scan the IT domain and find and verify the bugs.
Information Analysis And Planning : In this the stage examines the identified vulnerabilities . This is to come up with a design for penetrating into the network and systems
Privilege Escalation : It is the act of Using the vulnerabilities, planning the configuration failure in a PC or application software to achieve raised access to resources that is already secured from an application user.
Result analysis : Uncovering the the flaws in a Network, system and application and analysing the threats in it.
Reporting : Result from VAPT testing is to be examined and Documented for further use and clarification. This deals with the grade of threats that to be mensioned.
Cleanup : Clearing the bugs that found in the result analysis and making the roots of the application or network in a proper way.
LEVELS OF VULNERABILITY ASSESSMENT AND PENETRATION TESTING
* Testing the Security
* Security Assessment and review
* Auditing the security
TESTING THE SECURITY
Vulnerability assessment:
* Finding the Endpoint IP and Network Leakage Detection
* Rogue and Unknown Network Detection
Penetration testing:
* Network and system configuration reviews
* Environment vulnerability assessments
* Physical Security Review
SECURITY ASSESSMENT
* Security architecture, design and solutions review
* Security review of web-based systems:
* Applications security
* Database security
* Availability Assessment
* Distributed Denial of Service (DDoS) Protection
* Web Portal Availability
AUDITING THE SECURITY
* Active Directory (AD) Audit
* Window server And Workstation Audit
* Compliance audit
AD management
* Secure AD boundaries
* Secure domain controllers
* Physical security of the domain controllers
* Secure domain and domain controller configuration settings
* Secure administrative practices
“Privacy And Security Are really Important . You can’t have privacy without Security”
LEVELS OF TESTING IN VAPT
The basic security test take place on a systematic order. This include giving attention to the whole key security controls to protect the company. The scenario used for this needs to follow certain factors.
* Checks the avialability of security testing assets.
* Criticality of the system and the test controlled secured applications.
* Information responsiveness in the trialed systems and applications.
* Possibility of techincal failure of the mechanism.
* The chance of error that would threatn the security of the system.
* The risk and the rate of change of control configuration.
* Changes in the technical field that affects the control performance.
* The time and the trouble required to execute a contro test.
* the effect of test in a business operations.
After evaluating these areas of sources and risk, our security team plan and approve the comprehensive evaluation and testing methodology.
Vulnerability assessment
Vulnerability assessment deals with some procedures to do the normal vulnerability scan. This includes interpret, pinpoint, classifying and giving priority to vulnerabilities in a PC. More than this the applications and network infrastructures is considered to give awareness on risk in the threats and gives an idea to react at the right time.The vulnerability scanning tool should have the potential to equate the risk ranking based on best industry practices includes CVSS ( Common Vulnerability Scoring System). Also the the health check up of routers from the internet into the into the internal network , confined systems, web servers and critical servers.
Penetration Testing
Penetration testing also termed as ethical hacking or Pen Testing. In this the computer system is tested and finds bugs that can affect the whole system working. Also the test can be performed and automated with software applications or it allows to do manually.
The basic penetration Testing Areas in the IT infrastructure includes,
* Network: Identifying and discovering the security flaws in the network and systems.
* Web Application : The main focus is on searching threats in an applications that so far passed the primary stage.
* Mobile Applications : The main aim is to search for known attacks in the mobile applications.
* Wireless : This plans for known bugs in the Wifi Systems, Zigbee, RFID, NFC, Bluetooth, Z-wave, DECT,
* Contact less smart cards, and proprietary wireless systems.
The basic steps for penetration testing includes,
* Planning and exploration : Defining the scope and goals of a test
* Scanning : Includes both the static and Dynamic analysis .In the static analysis the application code at the time of running.The tools can be done in a single pass.
In the Dynamic analysis inspecting the application code in the running state. Real-time view in the performance of the application.
* Gaining Access : Web application attacks will be checked in this stage.This includes cross-site scripting, SQKL, injection and backdoors.
* Access maintaining: This stage the checking of vulnerability will be done in the exploited system.
* Analysis : The result will be displayed in this section. It includes,
– Specific vulnerabilities
– Sensitive Data that already accessed
– The time taken for a pen tester to be able and in the system undetected
The mostly used Penetration Testing methods are,
* External Testing
* Internal Testing
* Blind Testing
* Double blind Testing
* Targeted Testing
SECURITY ASSESSMENT
The aim of security assessment is to address known frailty and sort out the security issues.
The security architecture review performing areas include,
* Network topology, network division, and control of security devices located across the OSI networking structure.
* More than this Client based foundation.
* Server based infrastructure.
* Extensive parallel data system
* Distributed systems
* Cryptographic systems
* Industrial Control Systems
The areas of review occur mainly in three phases. Software development team performs the review in the web application during the development phase. Also software acceptance team perform the review in the integration and testing phase. More than this the security assessment team performs review in the production phase.
The DNS (Domain Name System) is a critical infrastructure for all infrastructure providers.The existance of a server unprotected to the internet ,The DNS server can be targetted by hackers to convert resource usage. An availability assessment give guarantee on the following :
* The efficacy of bugs propagation controls and protection tools will be scanned.
* The instantaneous control measures to avert Distributed Denial-of-Service (DDoS) and save against the volumetric attacks.
* Controls protecting critical servers and services
* Domain Name Service (DNS) management and DNS server protection.
SECURITY AUDIT
It is a special tool used for security completion process. The main Audit type includes Active Directory (AD) audit, Windows server and workstation audit and Compliance audit.
Active Directory (AD) Audit – Gives an analysis of AD execution security design productiveness to support the servers and workstations situated in a window environment.
Window server and workstation Audit – Gives the evaluation of functioning of servers (Web email,file/print). Also the performance of the operating system includes, Desktop, Laptop and other special applications.
Compliance Audit – Gives an evaluation of compliance with the existing policies, plan of actions, other standards and the operating effectiveness of security controls.
The Benefits Of VAPT
The bugs in an IT Infrastructure Can be sort out using VAPT. The main asset of Vulnerability Assessment and Penetration Testing includes,
* Giving the firm an idea about potential bugs faced by an application.
* Also helping an enterprise to find the errors in the programming that leads to Vulnerabilities.
* In addition to this provide threat management.
* More than this protecting the organization from money loss.
* Also securing the application from external and internal hacking.
* Also give protection against the malicious attack from destroying the organization data.